The science of chasing criminals
We’re familiar with this scenario from crime thrillers: One detective oversees an investigation, assisted by one or two colleagues. Case closed. But the days of two or three people working as a team have long become a thing of the past in real-world criminal investigations. Today, a wide variety of actors are involved in crime solving – as well as an increasing extent of digital technologies.
Der Experte
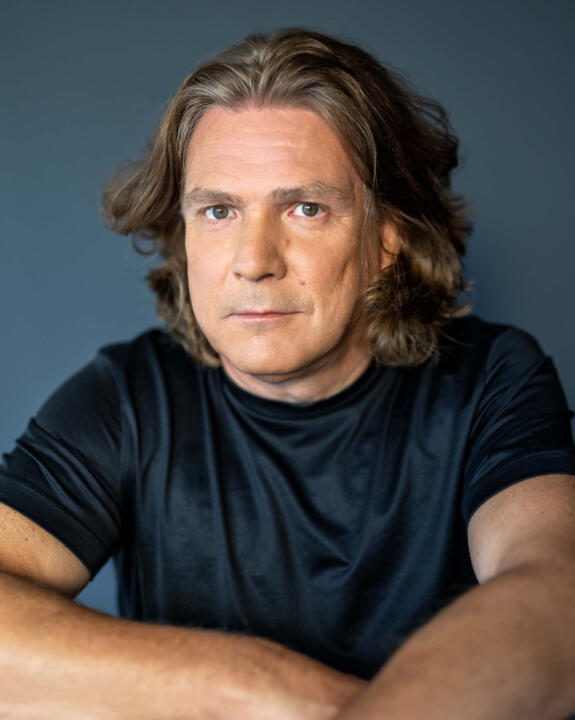
Dirk Labudde studied theoretical physics and medicine. Since 2009 he has been a professor of bioinformatics and digital forensic science at Mittweida University for Applied Sciences. As a consultant to various state-level police organizations and prosecutor’s offices, he assists with forensic solving of crimes and serves as an expert in court.
Forensic science is the driver of technological developments in criminal investigations. That discipline emerged toward the end of the 19th century when analysis and systematization of trace evidence increasingly became the focus of investigations. Before that, law enforcement officers would concentrate on witness statements, which – unlike scientific facts – were never objective, though. By contrast, forensic scientists define themselves as truth researchers. Based on verifiable information, they attempt to build a reality that will hold up in court. They analyze shoe and fingerprints, DNA traces, injuries, as well as traces of slashing and stabbing weapons or firearms.
A forensics team is as versatile as the range of courses offered by a university
Edmond Locard, a French physician and lawyer, is regarded as a pioneer in forensic science. Around 1910, he said, “Wherever he [the perpetrator] steps, whatever he touches, whatever he leaves, even unconsciously, will serve as a silent witness against him.” Today, perps also increasingly leave digital traces – whether with smartphones, PCs, in the cloud, or as GPS data – that need to be pursued.
“When you have eliminated all which is impossible, then whatever remains, however improbable, must be the truth.”
Hero of a novel Sherlock Holmes
Equally varied as trace evidence is the variety of skills found in forensic science. The motley teamwork encompasses physicians, natural scientists, computer scientists, mathematicians, anthropologists, geologists, and lawyers. Teams like to expand their perspectives by special skills such as those of game programmers and AI experts, depending on the case they’re working on. The objective of such comprehensive teamwork is to provide evidence of a perpetrator’s guilt and to have them indicted based on reliable forensic-science opinions. Creating those opinions resembles putting together a jigsaw puzzle with fluid pieces that keeps creating new pictures. In many cases, it takes weeks, months, or years to understand what really happened. In addition to professional knowledge, forensic scientists, above all, need patience. Hero of a novel Sherlock Holmes once put it this way, “When you have eliminated all which is impossible, then whatever remains, however improbable, must be the truth.” This sentence is a very fitting description of the process of establishing forensic hypotheses and verifying them across several iterations. The outcomes of those hypothesis-driven processes culminate in reconstructing how a crime took place. Forensic investigations, by the way, provide no clues about the perpetrator’s motive and resolve.
Digital twins of the crime scene and victim
Here’s an example of our field work at the Forensic Science Investigation Lab: In July 2019, a dead seventeen-year-old teenager from Germany was pulled out of the sea with a severe skull fracture at the Spanish tourist resort Lloret de Mar. The Spanish police assumed that he was drunk and fell into the sea from a cliff. In other words, an accident, but our forensic simulations showed that that was improbable. For the three-dimensional reconstruction of what took place we created digital twins of the cliff and the victim. In addition, we included the autopsy report, witness statements, the place in the sea where the body was found, and even the local current conditions in our analysis. From dozens of positions, we subsequently caused the virtual dummy to plunge from the coast. Just once it landed in water, albeit from a spot that was to be excluded based on the facts of the case. “When you have eliminated all which is impossible, then whatever remains must be the truth.” Sherlock Homes would have come to the same conclusions as my colleagues and I did: an accident as assumed by the police can be excluded in all probability. However, we couldn’t demonstrate how the teenager died either.
Digital race of good against evil
But before delving deeper into digital twin worlds, let’s briefly look back. From the 1990s on, the digital world evolved as a new crime scene and trace evidence. Computers became a mass product, the internet started its triumph, followed shortly afterward by smartphones. All that fundamentally changed people’s way of working and living. Naturally, criminals used and misused all the digital achievements as well. But it took a while for law enforcement agencies to start taking the digital world seriously as a crime scene and to think about that area in investigations as well. Since then, the race between cybercriminals, analog crooks with digital tool kits on the one side of the law and law enforcement agencies on the other side of the law has been taking place at an increasingly accelerated pace. But slow processes, data protection requirements, and a shortage of professionals keep giving perps an advantage. Consequently, compared to the analog world, it’s still much easier for criminals to get away unnoticed and with impunity in digital crime settings. But that’s currently changing …

The successful intrusion of French law enforcement officers into the encrypted communications channels of crypto smartphone provider EncroChat recently emphasized the digital clout of the police – including against analog gangs of criminals. For months, the investigators read chat histories, copied, and saved millions of data items. The French also took the Netherlands and the United Kingdom on board. When the eavesdropping mission was busted in summer of 2020 the police had long gathered enough information, leading to raids and arrests across Europe. Drugs, weapons, and contraband were confiscated – also in Germany, where Europol, the European police agency, had passed on the critical data to the Bundeskriminalamt (BKA). That rang in a turnaround in the digital fight against organized crime.
Although other crypto smartphone providers – such as Sky ECC, a crypto services provider based in Canada – filled the void the investigators soon struck again. Of its more than 170,000 clients worldwide 70,000 were bugged and the seized dataset is said to be four times as large as EncroChat’s. Again, hundreds of arrests followed and several tons of drugs were confiscated.
AI helps search for traces
IT forensic science – even though it’s still in a developmental stage – has a crucial part in these investigative successes and consistently extends its operational range. Currently, the lion’s share of case analyses there is focused on digital crimes and crime scenes, in other words on so-called cybercrime offenses such as data theft, digital blackmail, or crimes in the darknet like sending and sharing child pornography.
Generally, though, we must say that there are no pure cyber offenses. No criminal act begins and ends strictly on a computer. All of us, in other words perpetrators and victims, live in a world where a separation between a digital and real-world space is no longer possible. Every day, we use digital tools, leaving traces in the process that in the event of a crime must be secured and interpreted. The challenges with which investigators and IT forensic scientists are confronted in that regard are enormous because the data flood is huge and keeps growing: in addition to text messages, pictures and videos galore are shared within just one chat and must subsequently be analyzed. Terabytes of suspicious traces are found on confiscated data carriers like computers or smartphones – suspicious and criminal content must be differentiated from unsuspicious information. So far, people by and large analyze those data but it has long become an unreasonable effort – that’s why all over the world software solutions are in development with artificial intelligence inspecting and analyzing data. A South Korean research team, for instance, has developed the DarkBERT AI model that’s been trained with data from hackers and cybercriminals.
New methods are being added, frameworks are lacking
Another area of IT forensic science deals with digital methods to solve analog crimes because there are still plenty of those kinds of offenses as well. The analysis of the digital means of communications used by perpetrators and victims has long become standard practice. On the other hand, the digital twin used in the crime in Lloret de Mar is a case in point showing how modern technologies are going to decisively change case analyses at least as decisively as fingerprints and DNA comparisons did in the past.
In addition to true 3D representations of analog crime scenes and their trace situations on computers for simulations of how crimes took place, IT forensic science is working on other applications. For instance, photographs and videos can be reconstructed, enhanced, and analyzed in greater detail with digital tools. Today, it’s even possible to identify people in surveillance videos strictly based on their anatomy. What’s more, all we need is a skull to reconstruct faces of unidentified corpses in 3D models. In doing so, IT forensic science draws on the fundamentals of software that has been used for a long time in other fields such as architecture, gaming, and movies. Algorithms can now even be used to predict the highest probability of where and when a crime will be committed.
However, the legal frameworks enabling all that to be used as evidence in court are still largely lacking. To elaborate relevant regulations, it must be clear how exactly these systems work, how algorithms were programmed, and on what basis information is created. Data protection criteria must be complied with. Assessments of risks and consequences must be included in the development of such frameworks too
Another thing that’s often lacking as well is an awareness on the part of the investigators that any crime requires them to also think and focus on the digital life of perpetrators and victims. They’d have to know how to research and analyze those digital lives. They’d also need to know what digital resources are available for enhancing investigations. Reconstructions of crime scenes, simulations of how crimes were committed, and digital video and image analysis tools offer a wide variety of opportunities to verify hypotheses. Of course, it’s also up to us as forensic scientists to make that knowledge available to investigators. My vision of efficient, modern investigative work therefore consists of a new relationship between detectives and digital forensic scientists. What we need is well-trained experts from both camps with adequate knowledge of the work of the other party to work together closer than is normally the case today.


